Cyber Threat Hunting Guide: Techniques, Models, Tools, Benefits
Cybercriminals are growing more clever than ever before, making cyber threat hunting a crucial component of the network, endpoint, and data security measures. If a sophisticated external attacker or insider threat is able to circumvent basic network protection mechanisms, they may go unnoticed for weeks. During this period, they may collect sensitive data, breach private information, or get login credentials that allow them to traverse your network environment laterally.
To minimize the consequences of security breaches, it is crucial to detect them as soon as feasible. No longer can security professionals afford to wait for automated cyber threat detection systems to alert them of an approaching attack.
Cyber threat hunting is a proactive type of cyber defense. It is the proactive and iterative process of scanning via networks to find and isolate sophisticated threats that elude traditional security solutions. In contrast, standard threat management methods, such as firewalls, intrusion detection systems (IDS), sandboxes, and SIEM systems, often entail an assessment of evidence-based data after notification of a possible threat.
Cyber threat hunting helps the early identification of attacks by proactively identifying the behaviors of known and unknown adversaries using high-fidelity telemetry and the most recent threat data. It is an efficient approach for defending your company's IT networks and systems from cyber threats. A survey on the efficacy of threat hunting indicated that,
-
74% of responders mentioned fewer attack surfaces
-
59 percent reported improved reaction speed and accuracy
-
52 percent of organizations discovered previously undiscovered threats in their networks.
In this article, we will cover what cyber threat hunting is, how it works, the importance and benefits of threat hunting, threat hunting models and tools, challenges and best practices of threat hunting, and the required skills to be a competitive threat hunter.
What is Cyber Threat Hunting?
Cyber threat hunting, also known as threat hunting, is a proactive strategy to detect previously undisclosed or existing threats that have not been remedied inside a company's network.
Threat hunting is an aggressive technique based on the "assumption of the breach," which holds that attackers are already inside a company's network and are watching and moving stealthily across it. In practice, attackers may stay within a network for days, weeks, or even months without any automated security recognizing their existence, designing and executing attacks such as advanced persistent threats(APTs). Threat hunting thwarts these assaults by searching for hidden indications of compromise (IOCs) so that they may be reduced prior to achieving their goals.
Specifically, threat hunting responsibilities include:
-
Hunting for current dangers inside your business, including anything an attacker may exploit to exfiltrate data or inflict harm.
-
Proactively hunting for risks that may emerge anywhere in the globe
-
Setting a trap and waiting for potential attackers to find you
The main purpose of threat hunting is to try to find the following signs in the IT environment:
-
Host-Based Artifacts: Examine endpoints for malware involvement in the registry, file system, and elsewhere.
-
Network-Based Artifacts: Search for malware communication via session recording, packet capture, and network monitoring.
-
Indicators of Compromise (IOCs): Factors, such as forensics data and log files, that may assist in the identification of suspected harmful behavior that has already happened.
-
Indicators of Attack (IOAs): Although similar to IOCs, IOAs assist you to understand the occurring cyber attacks.
-
Adversaries: Based on their understanding of adversary motives and TTPs, threat hunters might seek indicators of adversary presence in an organization's environment.
How Does Threat Hunting Work?
Cyber threat hunting is effective because it combines the human aspect with the huge data processing capability of a software solution. Human threat hunters, whose purpose is to use solutions and intelligence/data to locate adversaries who may evade conventional defenses by employing techniques such as living off the land, rely on data from complex security monitoring and analytics tools to proactively identify and neutralize threats.
The cyber hunting process relies heavily on human intuition, strategic and moral reasoning, and innovative problem-solving. These human attributes allow enterprises to execute threat resolutions with more speed and precision than when using automated threat detection systems alone.
For cyber threat hunting to be effective, threat hunters must first create a baseline of expected or approved occurrences to discover abnormalities more effectively. Using this baseline and the most up-to-date threat intelligence, threat hunters may next examine security data and information gathered by threat detection technologies. These technologies may include security information and event management (SIEM), managed detection and response (MDR), and further security analytics tools.
Once threat hunters are armed with data from several sources, like endpoint, network, and cloud data, they may examine your systems for possible threats, suspicious activity, and triggers that depart from the usual. Threat hunters may create hypotheses and conduct in-depth network investigations if a threat is found or if existing threat information reveals new possible risks. During these investigations, threat hunters strive to determine if a threat is malicious or benign, as well as whether the network is appropriately protected against emerging cyber threats.
A cyber threat hunt consists of the following procedures or processes designed to make the search efficient and effective:
-
Hypothesis: The beginning of a threat hunt is a hypothesis, or a statement describing the hunter's beliefs about potential hazards in the environment and how to locate them. A hypothesis might comprise the tactics, techniques, and procedures (TTPs) of a suspected assailant. Threat hunters construct a logical route to detection using threat information, environmental knowledge, and their own expertise and inventiveness.
-
Collect and Process Intelligence and Data: Cyber threat hunting needs quality intelligence and data. A strategy is necessary for gathering, centralizing, and processing data. A Securityecurity Information and Event Management (SIEM) tool may give insight and a log of activity in an organization's IT environment.
-
Trigger: A hypothesis might serve as a trigger when sophisticated detection technologies direct threat hunters to investigate a particular system or network region.
-
Investigation: Investigative technology may seek or search deeply for possibly dangerous abnormalities in a system or network, determining whether they are harmless or malicious in the end. A threat hunter may rely on sophisticated and historical information obtained by threat hunting systems like SIEM, MDR, and User Entity Behavior Analytics (UEBA) throughout an investigation. The inquiry will continue until the hypothesis is verified and anomalies are identified, or until it is determined that the hypothesis is harmless.
-
Response/Resolution: Data obtained from malicious behavior that has been validated may be incorporated into automated security technologies to react, resolve, and reduce problems. Actions may include removing malware files, restoring altered or deleted files to their original state, updating firewall / IPS rules, deploying security patches, and modifying system configurations - all while gaining a better understanding of what transpired and how to improve your security against similar attacks in the future.
As hackers are always evolving and inventing new network risks, threat hunting is a never-ending endeavor. Alongside automated threat detection technology and your security team's existing threat identification and response methods, cyber threat hunting should become a daily habit inside your firm.
What are the Threat Hunting Models?
Threat hunters presume that enemies are already present in the system, and they conduct an inquiry to identify anomalous behavior that may signal hostile activity. In threat hunting, this inquiry initiation often falls into one of three categories:
-
Intel-based Hunting: Intel-based hunting is a reactive hunting technique that employs indicators of compromise from threat intelligence sources. The search then follows rules given by the SIEM and threat intelligence.
Intelligence-based searches may leverage indicators of compromise, hash values, IP addresses, domain names, networks, or host artifacts supplied by intelligence-sharing systems like computer emergency response teams (CERT). From these systems, an automated alert may be exported and imported into the SIEM as structured threat information expression (STIX) and trustworthy automated exchange of intelligence information (TAXII). Once the SIEM has received the IoC-based warning, the threat hunter may analyze the malicious activities before and following the alert to discover any environmental breach.
-
Hypothesis Hunting: Hypothesis hunting is a proactive hunting methodology that employs a threat hunting library. It conforms to the MITRE ATT&CK framework and uses global detection playbooks to identify malware assaults and advanced persistent threat groups.
Hypothesis-based hunting utilizes the IoAs and TTPs of attackers. The hunter detects threat actors based on the domain, environment, and attack behaviors used to generate a MITRE-compliant hypothesis. After identifying a behavior, a threat hunter will monitor activity patterns to discover, identify, and isolate the danger. Thus, the hunter can discover potential threats before they might do harm to an area.
-
Custom Hunting: Custom hunting is based on industry-standard hunting methods and situational awareness. It detects irregularities in the SIEM and EDR (Endpoint Detection and Response) tools and is adaptable to client needs.
Customized or situational hunts are undertaken proactively depending on conditions, such as geopolitical crises and targeted assaults, according to the needs of the customer. These hunting activities may use both intelligence- and hypothesis-based hunting models that include IoA and IoC data.
What is Threat Hunting Maturity Model?
The Hunting Maturity Model (HMM) is a basic model developed by security architect David J. Bianco for measuring the threat hunting capacity of an organization. It gives both a "where are we now?" statistic and a plan for program enhancement.
When evaluating an organization's hunting capability, there are three things to consider:
-
the quality of the data they gather for hunting
-
the tools they give to access and analyze the data
-
the capabilities of the analysts who utilize the data and tools to locate security events.
Among these variables, the analysts' abilities are perhaps the most crucial, since they are what enable them to transform data into detections. Therefore, each level of the Hunting Maturity Model (HMM) begins with a description of the normal degree of analytic competence at that level.
The quality of the regularly collected data from an organization's IT infrastructure is also a significant component in defining the HMM level. The greater the quantity and variety of data provided to a skilled hunter, the more results they will locate. The data collection and analysis tools are also components, although they are less significant. Given a high level of analyst talent and a huge quantity of high-quality data, it is feasible to partially compensate for toolset inadequacies. For this reason, each HMM level addresses the quality and quantity of data that is regularly gathered throughout the company but not the analytic toolset.
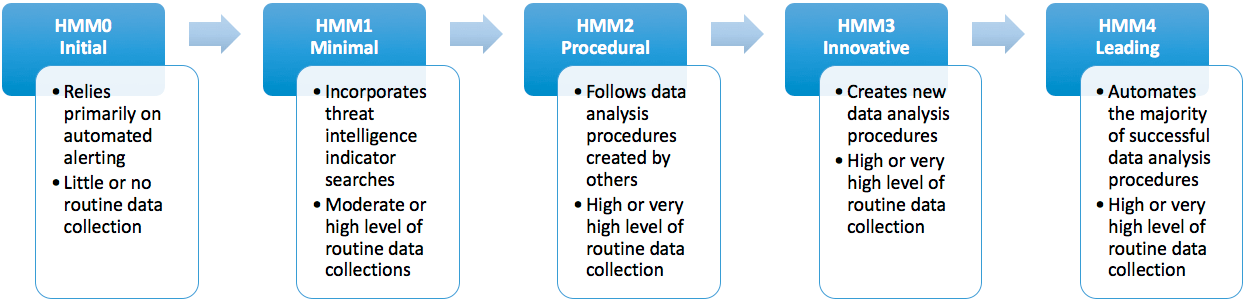
Figure 1. Hunting Maturity Model stages
The Hunting Maturity Model identifies five degrees of organizational hunting capability, from HMM0 (the least capable) to HMM4 (the most capable) (the most). Let's analyze each stage in depth.
HMM0 - Initial
At HMM0, a business largely uses automated alerting solutions like IDS, SIEM, and antivirus to identify harmful activities throughout the enterprise. . They may integrate signature update feeds or threat intelligence indicator feeds, and they may even generate their own signatures or indicators. However, they are supplied directly into the monitoring systems. Human activity at HMM0 is focused mostly on the resolution of alerts.
In addition, HMM0 firms gather less information from their IT systems beyond what is required to trigger their automatic alerts. Thus, even if they suddenly acquired hunting knowledge (by hiring a consultant or making a strategic hire, for example), their capacity to hunt would be severely constrained.
At HMM0, organizations are not deemed capable of hunting.
HMM1 - Minimal
An enterprise at HMM1 continues to rely mostly on automated alerts to drive their incident response process, but they do at least do regular IT data collection. These firms often want intelligence-driven detection (that is, they base their detection decisions in large part on their available threat intelligence). They often monitor the most recent danger alerts from both open and closed sources.
HMM1 businesses usually gather at least a few kinds of enterprise-wide data, and some may collect a great deal. Thus, when analysts become aware of new dangers, they may extract the important indications from these reports and review historical data to see whether they have been observed in the recent past.
Due to these search capabilities, HMM1 is the first level where hunting occurs, although in a small capacity.
HMM2 - Procedural
If you search the Internet for hunting techniques, you will get many excellent results. Typically, these processes combine an anticipated kind of input data with a specialized analytic methodology to identify a certain type of harmful behavior (e.g., detecting malware by gathering data about which programs are set to automatically start on hosts across the enterprise and using least-frequency analysis to find suspicious binaries). Organizations at the HMM2 maturity level can learn and use procedures produced by others and make modest modifications but are not yet capable of developing whole new processes.
HMM2 organizations implement these practices consistently, if not on a fixed timetable, then at least regularly.
The majority of frequently accessible techniques depend on least-frequency analysis (as of this writing, anyway). This method is only successful when there is data from several hosts. Consequently, HMM2 enterprises often gather a substantial (sometimes extremely large) quantity of enterprise-wide data.
The HMM2 capability level is the most prevalent among corporations with active hunting operations.
HMM3 - Innovative
These companies have at least a few hunters that are proficient in a range of data analysis methods and can use them to uncover malicious activities. As opposed to depending on methods created by others (as is the case with HMM2), these groups often design and publish their own. Analytical abilities might be as elementary as elementary statistics or as complex as linked data analysis, data visualization, or machine learning. The critical aspect is that the analysts can use the methodologies to establish documented and often executed repeatable processes.
Data gathering at HMM3 seems to be comparable to that at HMM2, but probably more sophisticated, since the analysts' concentration on creating new approaches over time tends to lead them to new data sources.
HMM3 organizations can detect and counteract threat actor behavior with great efficacy. As the number of hunting processes they build develops over time, companies may encounter scalability issues if they do not expand the number of available analysts.
HMM4 - Leading
An HMM4 organization is largely identical to an HMM3 organization, except automation. At HMM4, all successful hunting processes will be operationalized and automated detection will be implemented. This frees analysts from the pressure of repeatedly executing the same procedures, allowing them to focus on refining current processes or developing new ones.
HMM4 groups are very resistant to hostile activities. The high degree of automation enables them to concentrate their efforts on generating a steady supply of new hunting procedures, resulting in the continuous development of the whole detection software.
What is the Relationship Between HMM and Automation?
When developing new hunting strategies, an HMM4 organization will always prioritize automation. HMM0 companies, however, depend solely on their automated detection, whether it is provided by a vendor or developed internally. They may spend time enhancing their detection by establishing new signatures or searching for new threat intelligence streams to ingest, but they are not fundamentally altering how they identify attackers in their network. Even if they deploy the most powerful security analytics tools available, they are not hunting if they sit back and wait for alarms.
On the other hand, HMM4 organizations are actively experimenting with novel techniques to identify threat actors in their systems. They constantly attempt new ideas, knowing that some will fail while others will succeed. They are innovative, inquisitive, and nimble-traits that a completely automated detection product lacks. Although a decent hunting platform might give your team a boost, you cannot buy your way into HMM4 with money.
What are Threat Hunting Tools?
A successful threat hunting team must have access to the proper equipment. Threat hunters must be able to analyze vast quantities of data to spot patterns and decide whether or not particular events have happened. In many instances, the sheer amount of data involved makes human processing impractical or impossible.
As part of their job, threat hunters may use a wide range of tools. However, they use three distinct kinds of tools:
-
Analytics-driven tools, such as machine learning and behavioral analytics,
-
Intelligence-driven tools, such as malware and ransomware analysis, vulnerability scans, and threat intelligence reports
-
Situational-awareness tools are designed to add layer of security to any business-critical data or assets.
There are several open source and commercial threat hunting tools, and when they are combined, a formidable defense against cyber attacks may be constructed.
Free threat hunting tools are listed below:
- CyberChef
- Phishing Catcher
- AttackerKB
- dnstwist
- Maltego CE
- Cuckoo Sandbox
- Automater
- YETI
- AIEngine
- BotScout
- YARA
- CrowdFMS
- Machinae
- APT-Hunter
- Sysmon
- DeepBlueCLI
The following are some of the most popular paid threat hunting tools:
- Infrocyte
- Vectra
- Sqrrl
Why Threat Hunting is Important?
The importance of threat hunting stems from the fact that complex attacks may evade automated protection. Although automated security tools and security operations center (SOC) analysts should be able to handle around 80 percent of attacks, organizations still need to be concerned about the remaining 20 percent. The remaining 20% of threats are more likely to be sophisticated and capable of causing severe harm. Given sufficient time and money, they will break into any network and remain undetected for an average of 280 days. Effective threat hunting reduces the time between an intrusion and its detection, hence limiting the amount of harm perpetrated by attackers.
Typically, attackers hide for weeks or even months before being discovered. They calmly wait to exfiltrate data and unearth suengain more access, so laying the groundwork for a large data breach. According to the "Cost of a Data Breach Report", the average cost of a data breach to a corporation is about $4 million. And the negative consequences of a breach might last for years. The more time that elapses between a system breakdown and a reaction, the more expensive it may be for an organization.
What are the Benefits of Threat Hunting?
Threat hunting is a proactive activity that accompanies threat discovery and helps security teams to achieve crucial objectives, by providing the following advantages:
-
Vulnerability Management: Vulnerability management is difficult for any business owing to the complexity of corporate IT infrastructures and the large number of vulnerabilities found in production software. Threat hunting may aid in the detection and remediation of vulnerabilities inside an organization's systems that were previously undiscovered.
-
Intrusion Detection: Proactive threat hunting is crucial because it helps firms to uncover threats that evade current security measures. By searching for unnoticed intrusions, a threat hunter may uncover and eliminate security occurrences that pose a threat to the organization.
-
Streamlined Threat Detection: The majority of security teams are overloaded with data, which may impede threat detection and response. Threat hunters may discover more effective methods for collecting and analyzing data to detect diverse risks, allowing them to simplify threat detection and reduce the acquisition of unneeded data. Through threat hunting, both the mean time to detect (MTTD) and the mean time to respond (MTTR) to threats may be considerably decreased. By proactively finding security events and revealing holes in threat visibility and coverage, threat hunting may assist organizations in defending their most valuable assets and reputation.
-
Improved Cyber Defense: There is no such thing as flawless cybersecurity, and a business may not be gathering or analyzing the necessary data to identify different cyber threats. Threat hunting may aid in the identification of detection gaps and the development of tactics for gaining insight into further cyber threats.
-
Risk Management: Risk management is the foundation of cybersecurity, and a successful risk management program requires accurate data on the efficacy of the organization's cyber defenses. Threat hunting may contribute to risk analysis by assessing a company's susceptibility to cyber-attacks.
Threat hunting must be an integral part of any enterprise's security strategy. By gathering and analyzing data from several sources, threat hunters may detect significant visibility gaps and unearth previously undisclosed risks in corporate settings.
What are the Challenges of Threat Hunting?
Threat hunting is a time- and resource-intensive process and requires comprehensive knowledge of network and endpoint detection technologies, as well as adversarial tactics, techniques, and procedures (TTPs). Building a hunt team and equipping them with the requisite technology and intelligence is challenging for all but the biggest organizations. Because cyber security hunting requires a proactive, hands-on approach to threat identification and response, applying this security activity presents considerable obstacles for certain businesses.
The primary obstacles that threat hunting teams face are listed below:
-
Complex Threats: Modern threats are very sophisticated. Since threat actors may change assaults on the fly, analysts must search dynamically for tactics, techniques, and procedures (TTP).
-
Data Expansion: High rates of data expansion and organizational silos hinder the visibility of security operations centers. This is exacerbated by the ongoing addition of new apps and services, which increases the attack surface.
-
Slow Requests: Running searches against large quantities of data might impede response times. Due to scalability and speed limitations, some conventional systems might take hours to complete a query, jeopardizing an organization's capacity to recognize and react to threats.
-
Absence of Context: Threat hunting needs relevant context to reliably detect indicators of compromise, but connecting the dots across petabytes of data and many point products may be challenging and time-consuming.
-
High Price: Costs associated with licenses and data storage make it prohibitive for the majority of SOCs to gather and retain all security data for real-time and historical analysis.
Threat Hunting Best Practices
Threat hunting may be a helpful tool for enterprise cybersecurity, but only if the threat hunting program is effectively developed and executed. Threat hunting best practices include the following:
-
Automate When Possible: The immense quantity of data that threat hunters must gather, consolidate, and evaluate makes automation an essential tool. Threat hunters may use a variety of specialized platforms and tools for threat hunting to speed and simplify the process. Automation may aid in creating hypotheses and focusing the attention of threat hunters in addition to data collecting. Using artificial intelligence (AI) and user and entity behavioral analytics (UEBA), for instance, may aid in spotting anomalous occurrences that need examination.
-
Obtain Specialized Hunting Equipment: Effective and efficient threat hunting involves the capacity to swiftly confirm or refute assumptions about organizational threats. This requires the capacity to swiftly collect and evaluate information from several internal and external sources.
Although threat hunters may manually gather this information, it is time-consuming and requires a high level of knowledge and skill. Investing in specific security solutions, such as a SIEM and dark web monitoring service, may significantly accelerate the process of threat hunting.
-
Prioritize Based on Risk: Threat hunters may explore a variety of possible organizational threats. An organization always has more possible hypotheses to test than time and resources to examine. It is essential to prioritize threat hunting investigations depending on the possible danger to the company while organizing them. Risks have varying degrees of likelihood and possible influence on a business. Focusing on likely and high-risk threats maximizes the organization's gain from the search.
-
Specify a Specialized Threat Hunting Team: Infosec states, "Hunting can involve both machine-based and manual techniques. Unlike other automated systems, such as SIEM, hunting involves human capabilities to hunt threats with more sophistication."
The cyber threat hunting team is, perhaps, the most crucial element. Today's threat hunters must be specialists in the threat environment and able to immediately recognize the warning signs of advanced attacks.
The roles of security teams are diverse. Infrastructure protection, investigation of alarms, and other tasks are the responsibility of autonomous teams. If the security and IT teams are the same teams, they are allocated additional tasks. Due to its emphasis on hypotheses rather than real dangers to the organization, threat hunting may seem less essential. However, proactive investigations are essential for spotting dangers that are more complex and unknown. Defining a specific threat hunting job or a minimum number of threat hunting hours per week is necessary to ensure that threat hunting is completed.
-
Develop the Appropriate Abilities: Threat detection involves several skill sets. Threat hunters must be able to establish and evaluate hypotheses about possible organizational dangers. To execute these tests, they must also have extensive expertise and experience with the different platforms inside an organization's ecosystem. The success of a threat hunting team is strongly dependent on the available skills. Whenever feasible, take measures to recruit or train personnel with the required skill sets to conduct in-depth examinations of the business environment.
-
Have Comprehensive Data: To effectively search for threats, threat hunters must have access to an abundance of data (both current and historical data) that gives visibility throughout an organization's complete infrastructure. Without this aggregated data, threat hunters will be unable to generate educated threat hypotheses based on the organization's network and cloud infrastructure.
-
Have up-to-date CTI: Threat hunters must be provided with the most up-to-date threat information, allowing them to compare current cyber attack patterns with internal data. Without knowledge about emerging or trending risks, threat hunters will be unable to examine possible network threats accurately.
What skills must a threat hunter have?
A threat hunter is a cyber detective who identifies flaws in the IT security system of a business. Using a mix of human and machine-assisted tactics, threat hunters explore an organization's IT infrastructure for indications of compromise (IOCs). Frequently, threat hunters use the principle of assumed compromise to discover intrusions by hypothesizing about threat behaviors.
According to Infosec,
"Cyber threat hunting can be quite similar to real-world hunting." It requires a uniquely skilled professional possessed of considerable patience, critical thinking, creativity, and a keen eye for spotting prey, usually in the form of network behavior abnormalities."
In general, hunting is more of an analytic function than an engineering one. The major skills that a threat hunter must have are as follows:
-
Data Analytics: Threat hunters depend on technology to monitor their surroundings and gather logs and other data to do data analytics. Consequently, threat hunters must have a comprehensive grasp of data analytics and data science methodologies, tools, and strategies. Utilizing best practices such as the use of data visualization tools to build charts and diagrams substantially aids threat hunters in identifying trends, allowing them to establish the optimal course of action for performing threat-hunting operations and investigations.
-
Pattern Recognition and Deductive Reasoning: Persistently, attackers develop new and inventive methods to exploit vulnerabilities in popular operating systems and apps. Unanticipated zero-day vulnerabilities with no signatures are virtually a daily occurrence; hence, threat hunters must search for patterns that match the strategies, methods, and processes of recognized threat actors, sophisticated malware, and unexpected behaviors. To recognize these patterns, a trained threat hunter must also be familiar with regular network activity and patterns. In addition, they must be able to construct and build logical ideas about how to enter a network or abuse a system to acquire access to particular, crucial information. Once they have formulated their idea, they must be able to use deductive reasoning to move backward and identify possible traces and evidence left by attackers in certain circumstances.
-
Communication: Communication is a crucial component of an efficient threat-hunting team. Once a threat hunter identifies a danger, vulnerability, or weakness inside the corporate network, he must successfully convey this information to the proper stakeholders and employees to address and mitigate the problem. Attackers will continue to have the upper hand if threats and associated risks are not effectively conveyed to the appropriate stakeholders. Additionally, threat hunters must be adept at drafting reports and teaching people about threats and hazards. To aid management in making sound choices based on their results, teams must be able to explain their findings in plain language.
-
Malware Analysis/Data Forensics: When threat hunters discover new threats, they are frequently required to analyze and reverse engineer newly discovered malware and conduct data forensics to determine how the malware was initially deployed, its capabilities, and the extent of any damage or exposure it may have caused.
-
Deep Knowledge about IT Infrastructure: A threat hunter must have a comprehensive awareness of how the systems in the environment interact. Practical knowledge is derived from a thorough understanding of your business and its processes. Threat hunters must be able to examine a scenario and rapidly grasp its repercussions. Then, they should work with teams and aid them in enhancing security.
Which cybersecurity certification is needed to be a threat hunter?
Potential threat hunters may identify themselves with several qualifications, such as:
-
GIAC Cyber Threat Intelligence (GCTI) certification
-
GIAC Certified Forensic Analyst (GCFA) certification
-
Certified Cyber Threat Hunting Professional (CCTHP) certification
-
Certified Ethical Hacker (CEH) certification
-
CompTIA Security+ certification
What is the average salary of cyber threat hunters?
The average annual income for a cyber threat hunter in the United States is $136,525 or $70.01 per hour. Most experienced professionals earn up to $176,500 per year, while entry-level occupations begin at $116,000 per year.
What's the Difference Between Threat Hunting and Threat Intelligence?
According to Gartner:
Cyber threat intelligence is evidence-based knowledge (e.g., context, mechanisms, indicators, implications, and action-oriented advice) about existing or emerging menaces or hazards to assets.
Threat intelligence is often gathered and evaluated by automated security systems using artificial intelligence and machine learning. You may use cyber threat intelligence to take response to cyber-attacks and defend yourself from them. In lieu of manually allowing or refusing access, monitoring harmful threats, and documenting previously discovered criminals, cyber threat intelligence allows the execution of universal automated actions. Whenever a malicious attempt is found, it is immediately halted on all networks throughout the globe.
Threat hunting uses this knowledge to conduct a comprehensive, system-wide search for malicious actors. In other words, threat hunting starts with the conclusion of threat intelligence. In addition, an effective threat hunt might reveal risks that have not yet been seen in the wild.
Additionally, threat hunting employs threat indicators as leads or hypotheses for a hunt. Indicators of threat are the digital traces left by an attacker or malware, such as phishing emails, or other anomalous network activity.